eCrime eXchange (eCX)
The Industrial Event-Data Clearance Utility for Counter-Cybercrime Developers, Responders, Investigators, Underwriters and Cyber Risk Managers. eCX: Stewarding the Longitudinal Stability of Cybercrime Event Data — since 2004

APWG's eCrime eXchange (eCX) is the oldest and most trusted repository purpose-built for cybercrime event data exchange. In its operational objective and data fidelity architecture, eCX is a sectoral risk data clearinghouse for the curated exchange of cybercrime-related machine events, Internet events and those meta-data essential to forensic routines and security/counter-fraud applications.
eCX's architectural conceit places the globally recognized clearinghouse in an echelon with underwriters' property & casualty event data archives; maritime piracy event clearinghouses; and public health agencies' strain data archives — risk event data exchange models categorically and historically distinct from inauditable, ad hoc threat feeds typical of the cybersecurity domain.
Animated by this time-tested data fidelity framework, the eCX currently maintains cybercrime related machine-event data and Internet-event data endpoints on its API for six distinct data/event types, delivering billions of data field elements per month outbound to its members in the four corners of the globe through the eCX API.
eCX’s data fidelity architecture employs trust principles proven by underwriters’ claims archives, maritime piracy event clearinghouses, and communicable disease archives — risk-data exchanges categorically distinct from ad hoc feeds
eCX's trust instrumentation—legal governance; semantic discipline; and report record provenance tracking—maintained in a single curated system provides a keystone resource of rationally trustable cybercrime event data for industries and enterprises engaged in the cybersecurity domain.
Data Logistics & Governance Undergird eCX's Semantic Discipline
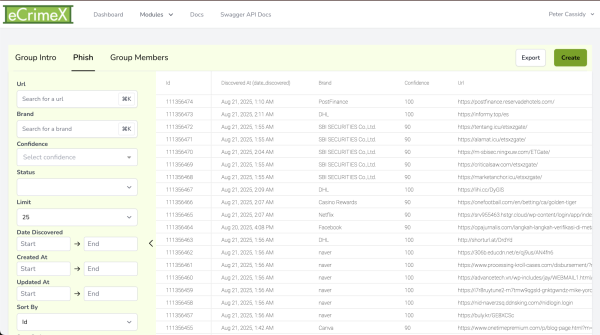
APWG member organizations contribute new data and extract archived records to inform products, services and research programs as well as to drive security applications and forensic routines, leveraging eCX's Confidence Factors and deeply defined record schema to make precision-dependent decisions on data integration and event reporting. (eCX offers a RESTful API for programming environments as well as a fully featured Web UI for researchers and responders to query eCX data sets as well as to submit their own reports.)
Submitting data into the eCX protects both member organization’s users and the wider public. Data reported to the eCX are immediately available to eCX users, including browser developers and security vendors who use the data to block phishing and responder / investigator organizations working to prevent attacks and halt criminal campaigns.
Entries are consistently categorized with fresh, reliability rated (with numeric Confidence Factors) data records flowing in continuously. Taxonomic fidelity of submissions by APWG members into eCX is also actively enforced as the foundational curational remit for this global clearinghouse - since 2004.
The event data types that APWG eCX archives for exchange between its corresponding members are as follows with more detailed descriptions in a table at the end of this page:
Phishing URLS:
Phishing eMails’ text, images and header data.
Maliciously engaged IPs addresses
Maliciously registered domains names
Cryptocurrency wallet addresses deployed for criminal cash outs
Maliciously deployed SMS/Text messages’ numbers and meta-data
APWG eCrime eXchange fuses legal governance, semantic discipline and report record provenance tracking into a single, rigorously curated system
In this way, eCX's essential data fidelity architecture, emulates the discipline that undergirds underwriters' calculation of rational premiums; guides ships at sea around piracy trouble spots; and informs epidemiological interventions like the seasonal flu programs.
For these domains, as in programmatic cybercrime suppression, data accuracy and taxonomic fidelity aren't an option but the bedrock of a global response to predictable, persistent risks like cybercrime.
Sectoral risk data exchanges like eCX rely on the same trust instrumentation that eCX adapts to its curational mission as a cybercrime risk data exchange. These sectoral risk data exchanges and repositories are examples of policy-bound, semantically governed clearinghouses, a long-tenured institutional role that is separate and distinct from ad hoc sharing models employed in most cyber threat feeds, distinguished in substantive ways that redound to keystone operational efficiencies for cybersecurity routines and counter-cybercrime applications.
Sectoral risk data exchanges are similarly:
- Discipline-enforced: Data isn't just required to be parseable by the system; submissions must comply with the semantic frame;
- Licensed, or agreement-based systems, distinctly not public open feeds - by design.
- Specific usage rules governed by legal agreements: APWG's DSA and other clearinghouse agreements dictate exactly how data is shared and what object, property and relationship terms mean;
- Version-aware / provenance-bound: Each record has an origin trace to the submitter, and updates are tracked within a policy framework;
This plexus of trust instrumentation stands in contrast to many threat-sharing feeds (e.g., open STIX/TAXII endpoints, IOC repositories, commercial blacklists), which:
- May not enforce strict vocabularies;
- Often lack deep provenance auditing;
- Have weaker legal usage governance or none at all.
While underwriters' event data clearinghouses (e.g. ISO), seaonsal flu program data archivs (e.g. GISAID) and the APWG may not publish formal ontologies (e.g. in OWL or RDF, etc.), each of these sectoral risk data clearinghouse define semantically rigorous, controlled data models which are ontology-like in practice by maintaining schemas governing how data elements are related, coded, and validated, even if not formalized in semantic web languages.
APWG's long-arc objective is for the stake-holding community to achieve the actuarial maturity required for civilization-level management of cybercrime risk
eCX, for the nonce, enforces its ontological model through traditional, rigorously detailed API schema and data conventions. Still, APWG is always considering the community of stakeholding data users and their ever-evolving needs as interveners, investigators and policy makers and other representatives of eCX data are always in development.
Sectoral Risk Exchanges Instrumentation Compared: APWG eCX / P&C Archives / Flu Strain IDs / Maritime Piracy Events
| Instrumentation | APWG eCrime eXchange | Property & Casualty Clearinghouses | DNA Sequence Archives | Maritime Piracy Clearinghouses |
|---|---|---|---|---|
| Data model type | Typed event-based model (phishing, IPs, etc) | Form-based, loss-event & actuarial data schemas (e.g. claims data) | Biological/genetic ID + metadata (e.g. DNA sequences) | Typed event-based model (piracy / armed; robbery; time; lat/long; vessel |
| Controlled vocabularies | Yes — threat types, brand targets, entity tags | Yes — cause of loss, policy class, geographic codes | Yes — clade names, hosts, variants, mutation codes | Yes — ship types, attack method, region, weapons |
| Provenance tracking | Yes — high-confidence reports tied to pre-registered entities | Yes — insurer ID and state regulator traceability | Yes — submitter name, lab, affiliation, country | Yes — vessel, flag state, reporting authority, IMO number |
| Immutable submission identity | Yes — each submission ID linked to DSA signer | Yes — required by trade organization rules & state legal statutes | Yes — (e.g. GISAID DAA), mandatory data field | Yes — incident / case ID logged in IMO (UN) / IMB (ICC) system |
| Confidence/quality score | Yes — per record, machine-readable | Indirect — via actuarial / statistical reliability | Partial — sequence quality scores + metadata checks | Indirect — factual reports, later verification; no machine-readable score |
| Change tracking/versioning | Yes — all record edits logged, authority restricted | Yes — versioned filings, statutory audit trails | Yes — updates logged, sequence revisions traceable | Yes — updates when more details confirmed; revisions logged |
| Legal framework governing data semantics | Yes — APWG Data Sharing Agreement (DSA) governs meaning | Yes — state/federal insurance code governs data meaning | Yes — (e.g. GISAID Data Access Agreement [DAA] enforces data use & terminology) | Yes — Maritime Law & IMO conventions (reporting obligations, ICC IMB practice) |
Proven Trust Schema Animates eCX Data Exchange
The eCX formally animates auditable cybercrime event data exchange by requiring contractual instrumentation and curation of data submission for all users. At once, this component of the eCX data fidelity architecture satisfies the risk-management requirements of corporate counsel — and incentivizes contribution of data of measurable reliability.
Bilateral data sharing requires corporate legal teams to forge agreements with everyone they want to share data with. That approach often requires years of legal work, and many times does not result in effective data sharing. This model of trust architecture also ensures that counterparties are vetted by the process itself, so that data consumed or sent can be verified as being from known parties, accountable by design.
APWG spent years refining a simple legal framework that allows data exchange to take place (among usually non-correspondent parties) while limiting and precisely defining the risk to submitters and receivers.
eCX Development Arc Over the Decades
The eCX and its progenitors have served the counter-cybercrime communities since 2004, initially distributing confirmed phishing URLs among APWG member companies and institutions, since expanding its purview to include six discrete cybercrime event types. [See: Data types table below.]
Currently, total report flow inbound to all endpoints on the eCX from all member sources numbers in the hundreds of thousands of new records per month from scores upon scores of institutions (many reporting on behalf of any number of enterprises and any number of client brands). Outbound flow of data elements from eCX to its users runs to billions per month through the eCX API.
As importantly, Arizona State University researchers found, in recent research, that eCX was alone in its class in one keystone metric: reports lodged at https://docs.apwg.org/documents/phishfarm_ieee_sp_2019_oest.pdf on the eCX generated the highest level of crawler traffic of any entity.[1]
Six event data types on eCX:
Phishing: The eCX receives hundreds to thousands of new, unique phishing URLs every day. The listings include confidence scores and brand (target) tags, so you can assess the data’s reliability. Learn about new attacks against hundreds of companies across the Internet, including the ones you need to protect.
Report Phishing: a repository of reported phishing emails, including header data, body text and images.
Malicious IPs: This feed contains IP addresses that have been recently observed as sources of malicious activity, such as fraudulent transactions and tell-tale port scanning.
Malicious Domains: An archive of maliciously registered domain names, including fake stores and fraud/identity theft websites. Supporting data can be added and forwarded to registrar and registry operators, or other APWG members, to aid in suspensions.
Cryptocurrency: This repository of problematic virtual currency addresses helps APWG members identify sources of malicious transactions and enrich your analytic tools. It’s high-value data for cryptocurrency exchanges, wallet providers, trading platforms, and investment funds who have to protect themselves and their customers against phishing and cybercrime. APWG members, to aid in takedowns.
Malicious SMS/Text: This repository of malicious text messages via SMS protocol and over-the-top text messaging service helps APWG members report and manage criminal texting.
| THE APWG ECRIME EXCHANGE IS AVAILABLE TO APWG MEMBERS VIEW THE ECX API DOCUMENTATION FOR MORE INFORMATION: APWG MEMBERS
|

[1]PhishFarm: A Scalable Framework for Measuring the Effectiveness of Evasion Techniques Against Browser Phishing Blacklists, in the Proceedings of the 40th IEEE Symposium on Security & Privacy, May 2019, San Francisco, CA. Adam Oest, Yeganeh Safaei, Adam Doupé, Gail-Joon Ahn, Brad Wardman, and Kevin Tyers.
https://docs.apwg.org/documents/phishfarm_ieee_sp_2019_oest.pdf