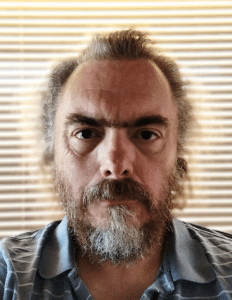
Speaker’s bio: Chema Alonso is member of Telefonica S.A. Executive Committee from 2016 and he is currently Chief Digital Officer. In this role, he oversees Innovation, Data, Platforms and Digital Product & Services leading the strategy for the digitalisation of sales processes and customer communication channels of the company. As head of this Global Unit, he also aims to promote innovation of new digital products and services as well as the generation of internal efficiency supported by the technological capacities of big data and artificial intelligence of Telefónica’s fourth platform, with special focus on the digital home. With a long background in the area of innovation, he is also responsible for the innovation of Telefónica’s core technologies as well as the company’s relationship with the entrepreneurial ecosystem under an open cooperation model. Contact info: mypublicinbox.com/ChemaAlonso
Paul Vixie serves as VP and Distinguished Engineer at AWS Security, and is a Director at SIE Europe U.G. He was previously the founder and CEO of Farsight Security (2013-2021). In addition, he founded and operated the first anti-spam company (MAPS, 1996), the first non-profit Internet infrastructure software company (ISC, 1994), and the first neutral and commercial Internet exchange (PAIX, 1991). Vixie was inducted into the Internet Hall of Fame in 2014 for work related to DNS, and is a prolific author of open source Internet software including Cron and BIND, and of many Internet standards concerning DNS and DNSSEC. He was CTO at Abovenet/MFN (1999-2001) and worked at DEC Western Research Lab (1988-1993) after dropping out of school in 1980. Vixie earned his Ph.D. in Computer Science from Keio University in 2011.
Effective modern site security is behavioral in nature. We cannot choose or exclude our endpoints nor validate their supply chains, and so to the extent that we manage digital risks posed by our endpoints we do it by watching the signals (packets and flows) they emit. Such observations are categorically untenable for investigative journalists and dissidents since the category is occupied by corrupt or authoritarian regimes or their national security apparatus — as explained by E. Snowden in 2013 and as codified by the IETF in RFC 7258. — Using the same protocols for mobile devices which accounted for most human-centric endpoint growth since 2010 as we do for fixed devices on networks controlled by families and businesses is disrupting our limited ability to secure the latter in order to defend against worst-case outcomes for the former. Several decades of unapologetic abuse by the powerful have led the IETF to reform the basic Internet protocol suite around TLS 1.3 with Encrypted Client Hello, DNS over HTTPS, and the replacement of TCP by the UDP-based QUIC protocol. — In this new configuration, network operators will not be able to detect endpoint behavior changes corresponding to infection, takeover, poisoned software update, latent design dangers, predaceous grooming, insider corruption, or hundreds of other well-understood digital harms. Many such operators have not been warned about this “rules change” and deserve to have their expectations explicitly and immediately reset so that they can make new plans which will be practical in the next era. It is the goal of this presentation to enumerate those alarms.

L. Jean Camp is a Professor in the School of Informatics, Computing and Engineering at Indiana University, in Informatics and Computer Science. For 2019, she is at University of California at Berkeley as a Visiting Scholar at the Center for Long Term Cybersecurity. She is a Fellow of the Institute of Electrical and Electronic Engineers. She is a Fellow of the American Association for the Advancement of Science, and has been inducted into the Sigma Xi honor society.
She joined Indiana after eight years at Harvard’s Kennedy School where her courses were also listed in Harvard Law, Harvard Business, and the Engineering Systems Division of MIT. She spent the year after earning her doctorate
from Carnegie Mellon as a Senior Member of the Technical Staff at Sandia National Laboratories. She began her career as an engineer at Catawba Nuclear Station with a MSEE at University of North Carolina at Charlotte. Her research focuses on the intersection of human and technical trust, levering economic models and human-centered design to create safe, secure systems. She is the author of two monographs. In addition, she has authored more than one hundred fifty publications. She has peer-reviewed publications on security and privacy at every layer of the OSI model.
Phishing is a ubiquitous global problem that is both the simple crime of theft of authenticating information and the first step in advanced persistent attack chains. Despite receiving worldwide attention and investments in targeted anti-phishing campaigns, a large proportion of people are still vulnerable to phishing. This is not only due to the evolution of phishing attacks, but also due to the diversity of those exposed to phishing attacks in terms of demographics, jurisdiction, and technical expertise. To explore phishing resilience, we conducted a cross-national study to identify demographic and other factors that might have an impact on phishing resilience across nations. Specifically, we recruited 250 participants from the United States, Australia, New Zealand, Canada, and the United Kingdom to observe their responses to phishing websites in a simulated environment. We identified how factors including demographics, knowledge, skills, website familiarity, and self-reported risk assessment behaviors relate to efficacy in phishing detection. While participants’ phishing knowledge, familiarity with the target website, and their reported use of the lock icon as a phishing indicator increases participants’ probability of correctly identifying a legitimate website, we found that these factors did not specifically make them more resilient to phishing attacks. Our results further show that computer expertise has a significant positive impact on phishing resilience and that increased age correlates with the probability of misconstruing a phishing site as legitimate. These findings were applicable across all five countries in our study.